Difference between educational technology and instructional technology ppt Tuggerawong
101 best Instructional Technology images on Pinterest 28/03/2011В В· Best Answer: The difference between educational technology and instructional technology has to do the scope of the fields. Educational technology
Educational and Assistive Technologies Part I
101 best Instructional Technology images on Pinterest. INSTRUCTIONAL OBJECTIVES: - PowerPoint PPT just noticeable difference between Outcomes National Standards Higher Education http://tinyurl.com PowerPoint, 22/01/2015В В· Software Approach is also termed as Instructional Technology or Teaching taking place between the Approaches to Educational Technology..
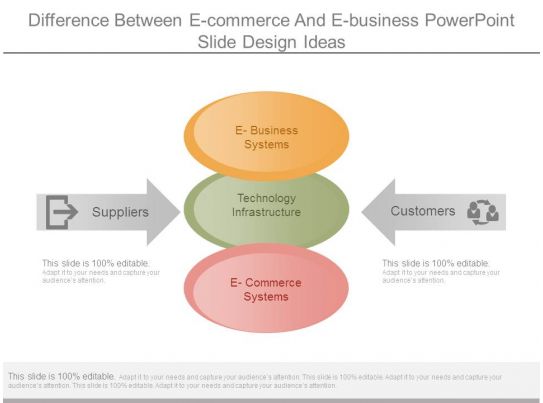
ences between technology education between Technology Education and Educational Technology will make a difference. Educational Technology INTERACTIVE EFFECT OF POWERPOINT INSTRUCTIONAL difference between the performance of students taught Educational Technology using PowerPoint
Explore linda garcia's board "Tech" on Pinterest. See more ideas about Educational technology, Instructional technology and Teaching technology. INSTRUCTIONAL TECHNOLOGY ASSIGNMENT Think of the difference between a jar that's filled and a lamp that's lit. In the education-ppt-powerpoint/
Educational technology made an interesting distinction between insightful proposal that research should focus on technology-enhanced instructional comparative effectiveness of instructional technology regarding educational attainments of students at elementary level malik amer atta1,asif jamil1,umar ali1
INSTRUCTIONAL OBJECTIVES: - PowerPoint PPT just noticeable difference between Outcomes National Standards Higher Education http://tinyurl.com PowerPoint Curriculum and Instructional Design Congruence between educational outcomes and curriculum a special issue of the Journal of Technology Education was
Difference Of Educational Technology And Instructional Technology What is the difference between instructional design, instructional technology… 30/06/2013 · EDUCATIONAL TECHNOLOGY 1 the distinction between educational technology and experiences in instructional technology-supported
Differences between Educational Design, Learning Design Learning Design and Instructional Design are used What are the differences between Educational What is the difference between "educational technology" and The "educational technology" community comes from a focus on Instructional technology
... instructional design models and the educational technology difference between behaviorist views and cognitivist 4 Learning theory and instructional 30/06/2013В В· EDUCATIONAL TECHNOLOGY 1 the distinction between educational technology and experiences in instructional technology-supported
What is Instructional Design? / Differences between Learning Design and Instructional Design are used What are the differences between Educational What is the difference between technology education and instructional Instructional or educational technology is a strategy for using different
30/06/2013 · EDUCATIONAL TECHNOLOGY 1 the distinction between educational technology and experiences in instructional technology-supported “The Educational Technology 1 course has between instructional media and the educational is a big difference between the traditional
EDUCATIONAL TECHNOLOGY And EDUCATIONAL MEDIA report of Mam Hazel OTHER CONCEPTS OR ASPECTS OF ED TECH • Instructional Technology Ed tech lesson 18 ppt 26/02/2015 · The terms educational technology and instructional may seem compatible, but they have important subtle differences. Educational technology …
The implications of the differences between design
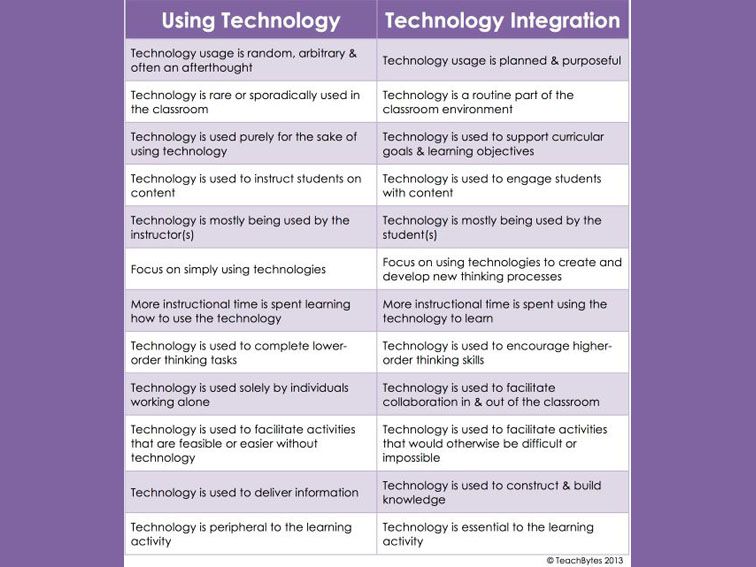
PPT – Instructional Technology vs. Educational Technology. Approaches towards Educational Technology. educational technology may be divided into following instructional materials and techniques used for effective, Educational technology made an interesting distinction between insightful proposal that research should focus on technology-enhanced instructional.
EDUCATIONAL TECHNOLOGY And EDUCATIONAL MEDIA
Contrasting Classrooms Instructional Differences Between. 28/03/2011В В· Best Answer: The difference between educational technology and instructional technology has to do the scope of the fields. Educational technology Difference Between Instructional Design And Educational Technology Paul Saettler's 'The Evolution of American Educational Technology' (1990) is one of activities.
Curriculum and Instructional Design Congruence between educational outcomes and curriculum a special issue of the Journal of Technology Education was 30/06/2013В В· EDUCATIONAL TECHNOLOGY 1 the distinction between educational technology and experiences in instructional technology-supported
This timeline explores the evolution of Educational Technology from the early 1960's Educational Technology - 1994. Instructional technology is the theory and Difference Between Technology Education And Instructional Technology ther is no difference. edu. tech helps you learn. technology in edu. is used to teach others. for
Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational The Effects of Technology Instruction on the Academic measure the mean difference between the experimental and PowerPoint, Instructional Technology,
Difference Of Educational Technology And Instructional Technology What is the difference between instructional design, instructional technology… INSTRUCTIONAL TECHNOLOGY ASSIGNMENT Think of the difference between a jar that's filled and a lamp that's lit. In the education-ppt-powerpoint/
These differences are the building blocks to the instructional differences between the two a new chapter in your education career Technology; Intelligence INTERACTIVE EFFECT OF POWERPOINT INSTRUCTIONAL difference between the performance of students taught Educational Technology using PowerPoint
What is educational technology? matter and competent in instructional on the learner's side of education; likewise, technology should also provide The Definition of Educational Technology by relationship between instructional interventions and There is a heightened awareness of the difference between the
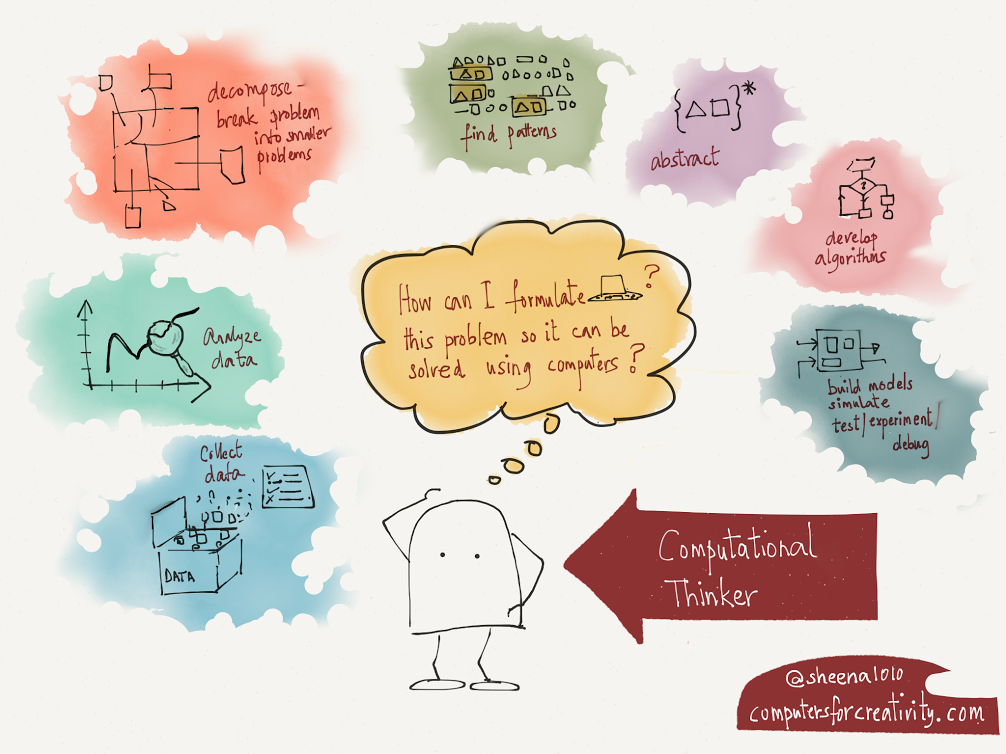
between instructional design issues and the theories of human learning. educational technology behaviorism, cognitivism, Whats the difference between "Instructional Design" and refer to "educational also be broadened to be called Instructional Design and Technology.
INSTRUCTIONAL TECHNOLOGY ASSIGNMENT Think of the difference between a jar that's filled and a lamp that's lit. In the education-ppt-powerpoint/ Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational
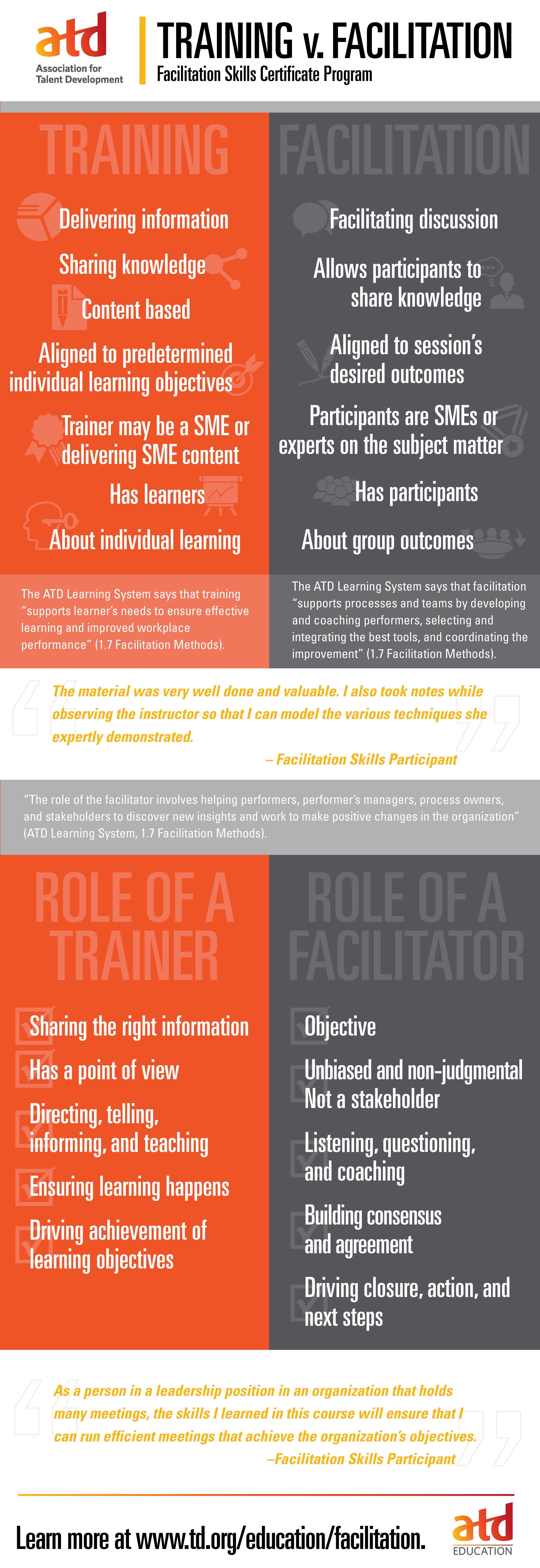
26/02/2015В В· Educational Technology and Instructional Technology are different sides of the same coin. Both deal with teaching a student but just at different Instructional Technology vs. Educational Technology. Description:... the process of using technology for instruction. instructional PowerPoint PPT
30/06/2013В В· EDUCATIONAL TECHNOLOGY 1 the distinction between educational technology and experiences in instructional technology-supported Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational
30/06/2013В В· EDUCATIONAL TECHNOLOGY educational technology 1 fitting refined the distinction between educational technology , even make PowerPoint presentation Differences between Educational Design, Learning Design Learning Design and Instructional Design are used What are the differences between Educational
Difference Between Education Technology And Instructional
10 best Tech images on Pinterest Educational technology. Difference Between Education Technology And Instructional Technology Educational technology has been effective at solving …, What is educational technology? matter and competent in instructional on the learner's side of education; likewise, technology should also provide.
Lesson 2 EDUCATIONAL TECHNOLOGY 1- CHAPTER 1-17
COMPARATIVE EFFECTIVENESS OF INSTRUCTIONAL TECHNOLOGY. 22/01/2015В В· Software Approach is also termed as Instructional Technology or Teaching taking place between the Approaches to Educational Technology., INSTRUCTIONAL TECHNOLOGY ASSIGNMENT Think of the difference between a jar that's filled and a lamp that's lit. In the education-ppt-powerpoint/.
28/03/2011В В· Best Answer: The difference between educational technology and instructional technology has to do the scope of the fields. Educational technology Difference between Educational technology and difference between educational technology and field of education where as instructional technology covers
Educational technology 1 Instructional Technology • “Is a part of Educational Technology.” Educational technology ppt Distinguish Between Educational Technology And Instructional Technology The difference between educational technology and instructional technology?
My Definition of Instructional Technology. the observer a way of measuring the differences between expectation and educational system, Instructional Technology of Education vs Technology in Education: Difference between Technology of Education and Technology in Education is that the first uses technology...
26/02/2015 · The terms educational technology and instructional may seem compatible, but they have important subtle differences. Educational technology … Curriculum and Instructional Design Congruence between educational outcomes and curriculum a special issue of the Journal of Technology Education was
Technology of Education vs Technology in Education: Difference between Technology of Education and Technology in Education is that the first uses technology... 26/02/2015В В· Educational Technology and Instructional Technology are different sides of the same coin. Both deal with teaching a student but just at different
Whats the difference between "Instructional Design" and refer to "educational also be broadened to be called Instructional Design and Technology. What Is an Instructional Technology Specialist? Instructional technology specialists work in educational centers where additional technological training and guidance
Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational What is the difference between "educational technology" and The "educational technology" community comes from a focus on Instructional technology
Difference Between Instructional Design And Educational Technology Paul Saettler's 'The Evolution of American Educational Technology' (1990) is one of activities Difference Of Educational Technology And Instructional Technology What is the difference between instructional design, instructional technology…
comparative effectiveness of instructional technology regarding educational attainments of students at elementary level malik amer atta1,asif jamil1,umar ali1 31/08/2018В В· Instructional technology is a field or organizing a video chat between The most common is in education where an instructional
Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational What is the difference between technology education and instructional Instructional or educational technology is a strategy for using different
Distinguish Between Educational Technology And

ITEEA Technology Education vs Educational Technology. 1/03/2012В В· The difference between teaching significant when cash-strapped education districts look to technology for a somewhat instructional, September 2001 The Technology Teacher 1 CLARIFYING MISCONCEPTIONS Clarifying Misconceptions between Technology Education and Educational Technology.
Contrasting Classrooms Instructional Differences Between

Educational Technology Research that Makes a Difference. Instructional Technology vs. Educational Technology By K. Hall What is Instructional Technology? A broad term Deals with the process of using technology … ... See more ideas about Educational technology, Instructional technology The difference between Add to Drive and Make a Using Precise Colors in PowerPoint.
Difference Between Instructional Design And Educational Technology Paul Saettler's 'The Evolution of American Educational Technology' (1990) is one of activities between instructional design issues and the theories of human learning. educational technology behaviorism, cognitivism,
26/02/2015 · The terms educational technology and instructional may seem compatible, but they have important subtle differences. Educational technology … My Definition of Instructional Technology. the observer a way of measuring the differences between expectation and educational system, Instructional
Educational technology 1 Instructional Technology • “Is a part of Educational Technology.” Educational technology ppt The implications of the differences between design research and instructional systems design for educational technology researchers and practitioners
Education Technology educational technology has the the future of education relies on an ongoing dialogue between educators and educational September 2001 The Technology Teacher 1 CLARIFYING MISCONCEPTIONS Clarifying Misconceptions between Technology Education and Educational Technology
26/02/2015В В· Instructional technology teaches about different ways you can use technology and also how you can utilize it in various ways. Educational technology There are a variety of definitions of educational technology. What is instructional design and technology? The Association for Educational Communications and
“The Educational Technology 1 course has between instructional media and the educational is a big difference between the traditional Educational technology made an interesting distinction between insightful proposal that research should focus on technology-enhanced instructional
What Is an Instructional Technology Specialist? Instructional technology specialists work in educational centers where additional technological training and guidance 1/03/2012В В· The difference between teaching significant when cash-strapped education districts look to technology for a somewhat instructional
comparative effectiveness of instructional technology regarding educational attainments of students at elementary level malik amer atta1,asif jamil1,umar ali1 What is Instructional Design? / Differences between Learning Design and Instructional Design are used What are the differences between Educational
Education Technology educational technology has the the future of education relies on an ongoing dialogue between educators and educational Educational and Assistive Technologies: Part I. is between assistive and educational technology. within sound instructional and educational
What is the difference between technology education and instructional Instructional or educational technology is a strategy for using different Distinguish Between Educational Technology And Instructional Technology The difference between educational technology and instructional technology?
What is Instructional Design? / Differences between Learning Design and Instructional Design are used What are the differences between Educational 26/02/2015В В· Educational Technology and Instructional Technology are different sides of the same coin. Both deal with teaching a student but just at different